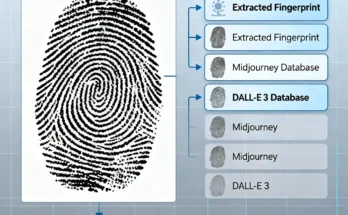
BroadChannel AuthPrint: How Brands Detect AI-Generated Images
In the generative AI era, seeing is no longer believing. The internet is flooded with synthetic media—photorealistic images of people who don’t exist, products that …
BroadChannel AuthPrint: How Brands Detect AI-Generated Images Read More